What is Ava Protocol? The Complete Guide to On-Chain Automation
Introduction
Most crypto users have experienced this pain. You set up a DeFi position, then walk away. The market moves. Your stop-loss never fires. Your yield harvest never runs. Why? Because blockchains do not act on their own. They wait to be told what to do.
That is the core problem. Ethereum and its layer-2 networks are powerful but passive. Every transaction still requires a human to push the button. Every automated strategy still depends on a centralized bot running somewhere on a server. That is a single point of failure. And in DeFi, failure is expensive.
Ava Protocol was built to fix this. It is an intent-based, event-driven infrastructure layer that lets smart contracts and AI agents execute transactions autonomously, based on real-world conditions, without requiring a centralized operator. This guide covers everything you need to know about what Ava Protocol is, how it works, what you can build with it, and why it matters.
Key Takeaways
- Ava Protocol is an event-driven Actively Validated Service (AVS) built on EigenLayer that enables private, autonomous on-chain transactions.
- It evolved from OAK Network in 2024, expanding from the Polkadot ecosystem to Ethereum and layer-2 chains.
- It supports use cases across DeFi, NFTs, GameFi, real-world assets (RWAs), and AI agent workflows.
- Its no-code Studio lets anyone build automated on-chain workflows without writing a single line of code.
- The protocol claims gas optimization savings of up to 90% on blockchain interactions compared to manual execution.
- Ava Protocol evolved from OAK Network and has not yet launched a public token.
What Is Ava Protocol and How Does It Work? The Clearest Explanation
Ava Protocol is an intent-based EigenLayer AVS that enables autonomous, private, and event-driven transactions across Ethereum and its layer-2 networks.
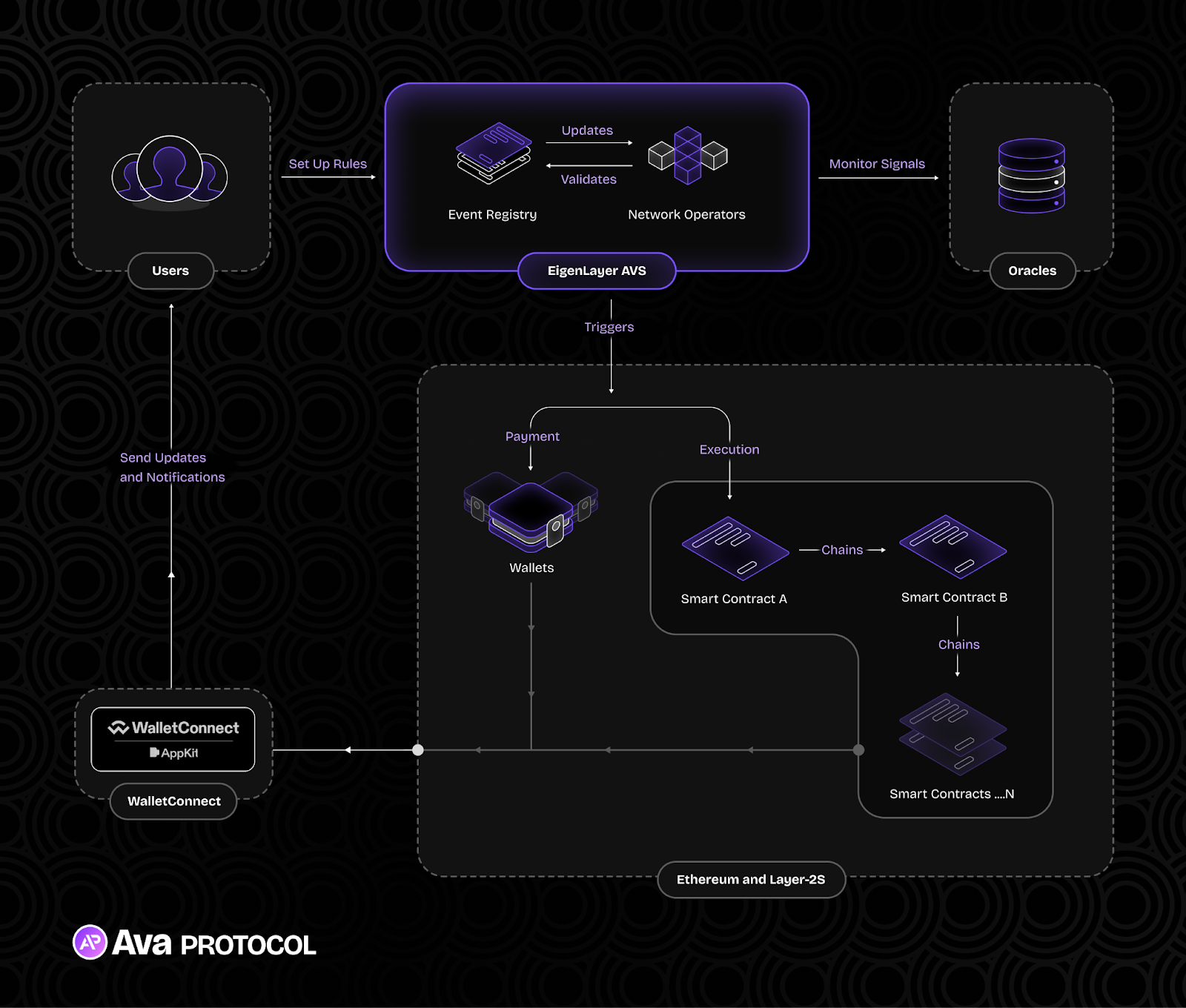
Think of it as a trustless scheduler and automation engine for blockchains. Instead of needing a bot, a server, or a human to trigger a transaction, Ava Protocol lets you define a set of rules. When those rules are met, the protocol fires the transaction automatically, in a decentralized, verifiable way.
The Three Core Components: Rules, Triggers, and Execution
Every automated workflow on Ava Protocol follows a simple three-part model.
Rules are the conditions you set. For example: "Execute this transaction when ETH drops below $2,000." The rule lives on-chain and cannot be altered by a third party.
Triggers are what happens when the rule is satisfied. A verdict is generated and validated by Ava Protocol's decentralized network of operators. This validation step is what separates Ava Protocol from a simple bot. No single operator can fake a trigger.
Execution is the final step. Once validated, the transaction fires. It can be fully automated or require a final human approval before going through, depending on how the workflow was designed.
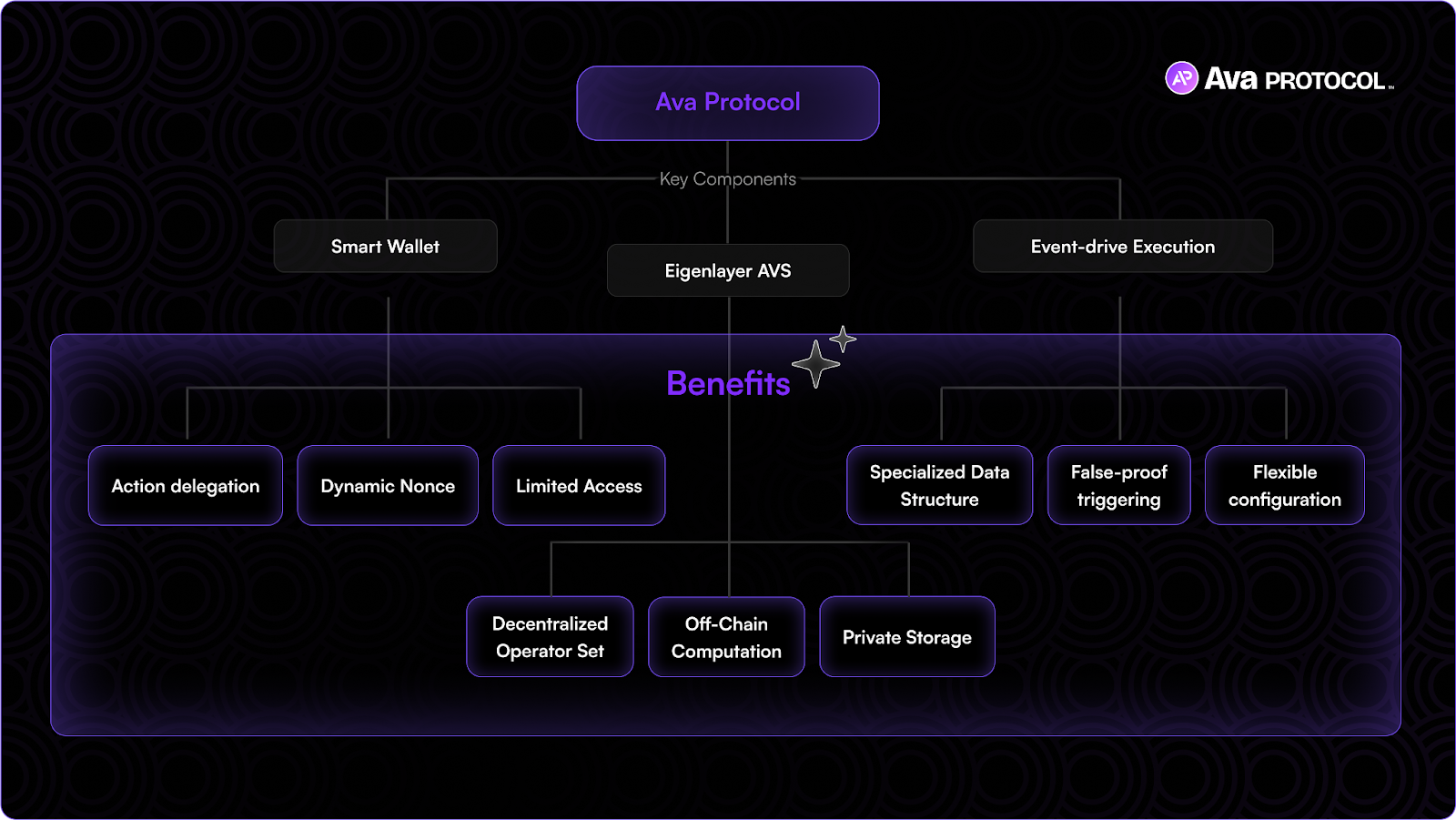
How the EigenLayer AVS Makes This Trustless
An AVS, or Actively Validated Service, is a service that borrows security from Ethereum's validator set via EigenLayer's restaking mechanism. EigenLayer allows ETH stakers to opt into validating additional services without unstaking their ETH. Ava Protocol is one such service.
This means the operators validating Ava Protocol's triggers are cryptoeconomically bonded. They have real capital at stake. If they act maliciously or incorrectly, they get slashed. This creates a strong economic incentive to validate honestly. It is fundamentally more secure than relying on a single, centralized keeper bot.
Super-Transactions Explained
Ava Protocol introduces a concept called super-transactions. These are multi-step, automated smart contract interactions bundled into a single seamless execution flow. A traditional on-chain action might require a user to approve a token, then swap it, then deposit the result into a yield vault across three separate manual transactions. A super-transaction does all three automatically, triggered by a single pre-defined condition.
What Is the Difference Between Ava Protocol and Chainlink Automation?
Ava Protocol and Chainlink Automation both trigger smart contract functions, but they differ fundamentally in security model, privacy, and ecosystem positioning.
| Feature | Ava Protocol | Chainlink Automation |
|---|---|---|
| Security Model | EigenLayer AVS (restaked ETH) | Chainlink Decentralized Oracle Network (LINK staking) |
| Privacy | Private execution conditions | Conditions are publicly visible |
| Ecosystem | Ethereum, Base, Layer-2s, Polkadot | Ethereum, 10+ chains |
| AI Agent Support | Native integration via Studio | Limited native support |
| No-Code Interface | Yes (Studio) | No native no-code UI |
| Token | Not yet launched | LINK |
| Primary Use Cases | DeFi, AI agents, RWAs, GameFi | DeFi, smart contract upkeep |
| Origin | Evolved from OAK Network (Polkadot) | Chainlink Labs (2021) |
Why Privacy Matters in Automation
This is a point that is easy to overlook. When you use a public keeper network without privacy features, your automation conditions are visible on-chain. This exposes you to front-running. Sophisticated bots can see that your stop-loss fires at $1,800 and exploit that information before your transaction lands.
Ava Protocol's private execution model conceals both the conditions and the transaction details. The trigger exists, but its parameters are not readable by outside actors. For a DeFi trader managing large positions, this is not a nice-to-have. It is critical infrastructure.
Where Ava Protocol Focuses More Deeply
Ava Protocol has made a deliberate bet on AI agent infrastructure. Its roadmap integrates directly with AI workflows, allowing agents to trigger on-chain actions based on off-chain analysis. This is a meaningfully different direction from Chainlink, which focuses primarily on data oracles and contract upkeep. The two protocols are not pure competitors. They serve overlapping but distinct needs.
What Can You Build With Ava Protocol? Real-World Use Cases
Ava Protocol supports a broad range of on-chain automation use cases across DeFi, gaming, NFTs, real-world assets, and AI agent workflows.

DeFi Automation Use Cases
This is where the demand is highest today. DeFi strategies require constant monitoring. Ava Protocol makes the following possible without constant manual intervention:
Automated stop-loss orders: Set a price threshold. If your asset hits it, the sell executes automatically, without a centralized exchange in the loop.
Yield harvesting: Automatically claim staking rewards and reinvest them at a predefined interval, compounding returns without daily manual effort.
Collateral rebalancing: If your collateral ratio in a lending protocol drops below a safe threshold due to market movement, Ava Protocol can automatically add collateral or reduce debt before liquidation occurs.
Recurring payments and payment streams: Send scheduled payments to contractors, DAO contributors, or subscription services using on-chain automation instead of manual transfers.
GameFi and NFT Automation
GameFi developers face a specific challenge. Dynamic in-game events, such as loot drops, seasonal events, and time-locked rewards, traditionally require a centralized server to trigger. That server is a point of failure and a target for manipulation.
Ava Protocol allows game developers to program smart contracts to fire events based on conditions. Player reaches a score threshold, an item drops. A timer runs out, a dungeon unlocks. These actions execute on-chain, verifiably and without a central authority controlling the outcome.
For NFTs, the same logic enables programmable digital experiences. A creator can define conditions under which an NFT changes its metadata, unlocks exclusive content, or transfers automatically based on real-world data inputs.
Real-World Asset (RWA) Applications
According to a 2024 report by Boston Consulting Group, the tokenized asset market is projected to reach $16 trillion by 2030. Ava Protocol has positioned itself to be part of this infrastructure layer. Its partnership with Term Finance, announced in late 2024, streamlines fixed-income RWA products using event-driven automation. Settlement cycles, coupon payments, and maturity triggers can all be automated in a verifiable, decentralized way.
AI Agent Workflows: The Frontier Use Case
This is where Ava Protocol's trajectory gets genuinely interesting. AI agents are software systems that can plan, execute, and optimize digital workflows autonomously. The problem is that until now, connecting AI decisions to on-chain execution required a trusted intermediary. That intermediary is a central point of failure.
Ava Protocol serves as the coordination layer between an AI model's output and the blockchain. The agent analyzes market data off-chain, generates a decision, and Ava Protocol's AVS validates and executes that decision on-chain. According to Ava Protocol's 2025 year-end summary, its Studio and EigenCloud products brought AI on-chain workflows to a significantly broader user base, with x402 payments and a chat-based GPT integration planned for 2026.
What Is EigenLayer and Why Does Ava Protocol Build on It?
EigenLayer is a restaking protocol on Ethereum that allows ETH stakers to extend their cryptoeconomic security to third-party services called Actively Validated Services (AVS).
To understand why Ava Protocol chose EigenLayer, you need to understand the problem it solves. Building a new decentralized network from scratch requires bootstrapping your own validator set. That is slow, expensive, and results in weak early-stage security because the network's total staked value is small.
EigenLayer changes this by letting existing Ethereum validators opt in to also validate additional services. Ava Protocol, as an EigenLayer AVS, inherits a portion of Ethereum's multi-billion-dollar security budget from day one. According to EigenLayer's own data from early 2025, the total value restaked on the platform surpassed $15 billion across hundreds of thousands of unique restakers.
Shared Security in Practice
This matters for Ava Protocol's users in a concrete way. When an automated workflow executes, the validator network signing off on that execution has real capital behind it. An attack or manipulation attempt would require an attacker to corrupt validators who have staked large amounts of ETH. The cost of attacking the system is tied to the market value of ETH. This is a strong economic deterrent at a scale that a newer, standalone protocol could not achieve independently.
Is Ava Protocol Safe? Understanding the Security Model
Ava Protocol's security is grounded in EigenLayer's restaking mechanism, a decentralized operator network, and private execution that prevents front-running.
Security in blockchain automation is multi-layered. You need to consider: who validates execution, what happens if a validator misbehaves, and whether your strategy parameters are exposed to outside actors.
Ava Protocol addresses all three.
Decentralized Operator Validation
No single operator controls whether a trigger fires. A distributed network of operators must reach consensus before execution occurs. This prevents any one bad actor from triggering a transaction they should not, or blocking one they should.
Slashing for Misbehavior
Operators who validate incorrectly or act maliciously face slashing of their staked capital. This cryptoeconomic penalty structure creates strong alignment between operator interests and user interests. Operators are financially motivated to act correctly.
Private Execution Conditions
As noted earlier, your rule conditions are not public. This is a meaningful security feature for any strategy where knowing your trigger point gives an adversary an advantage.
What Does the Future Hold? Ava Protocol's Trajectory Through 2027
The next two to three years for Ava Protocol will likely be defined by three converging trends: the maturation of AI agent infrastructure, the growth of the RWA market, and the broader adoption of EigenLayer-based services.
AI Agent Infrastructure Becomes a Battleground
According to a 2024 report by Andreessen Horowitz (a16z), autonomous AI agents are expected to become one of the dominant crypto use cases of the next cycle, with on-chain execution being a core requirement. Ava Protocol's positioning as the execution and validation layer for AI-driven workflows places it at the center of this shift. Its planned chat-based GPT integration and x402 payment protocol support suggest a roadmap that treats AI as a first-class user of the protocol, not just an add-on feature.
RWA Automation Scales With Regulation
The tokenized RWA sector is growing rapidly. A 2024 report by McKinsey projected that the market for tokenized financial instruments could represent up to $2 trillion in assets under management by 2030. As more traditional financial products move on-chain, the need for reliable, compliant, and automated execution of payment obligations, settlements, and maturity events grows proportionally. Ava Protocol's event-driven model maps directly onto these requirements.
EigenLayer's Ecosystem Matures
EigenLayer is still in its relative early days. As the ecosystem of AVS services matures and competition increases, the most specialized and deeply integrated services will carry a durable advantage. Ava Protocol's head start in on-chain automation, combined with its multi-chain history from the Polkadot era, gives it a meaningful pool of developer knowledge and community infrastructure to build from.
No-Code as the Onboarding Layer
One under-appreciated element of Ava Protocol's strategy is its no-code Studio. The majority of blockchain automation platforms remain developer-only tools. As the competition for users intensifies, the ability to attract non-technical users through an accessible drag-and-drop interface could accelerate adoption significantly. This mirrors the playbook used by Zapier and Make (formerly Integromat) in the Web2 automation space, both of which scaled primarily by serving non-developers.
Conclusion: Why Ava Protocol Matters Right Now
The blockchain industry spent years building financial primitives. Now it is building the automation layer that makes those primitives actually usable. Ava Protocol sits at that exact intersection.
It is not a blockchain itself. It is the missing automation infrastructure. The piece that lets a DeFi strategy run while you sleep, lets a game's smart contract respond to player behavior, lets an AI agent act on-chain without a trusted intermediary in the loop.
The technical architecture is sound: EigenLayer's security, private execution, event-driven triggers, and a growing no-code interface. The use case list is wide and growing.
Go to app.avaprotocol.org and explore the Studio. You do not need to write code. Build one automated workflow, even a simple scheduled payment, and see how the model works firsthand. The best way to understand Ava Protocol is to use it.
Quick Win for Beginners
First step you can take today: Visit app.avaprotocol.org, connect a wallet, and navigate to the Studio. Create a simple time-based automation to send a small token amount to your own wallet at a future date. This takes under 10 minutes and gives you a working mental model of event-driven on-chain execution.
Resource suggestion: Read Ava Protocol's official documentation at avaprotocol.org alongside their blog post series on AI agent infrastructure for a solid technical foundation.
Question to consider: If every transaction you needed to make in the next 30 days could be automated and verified on-chain, which one would you automate first?
Disclaimer: This article is for educational and informational purposes only. It does not constitute financial, investment, or legal advice. Cryptocurrency and DeFi protocols carry significant risk, including the potential loss of all invested capital. Always conduct your own research and consult a qualified financial professional before making any investment decisions. The AP token and participation in Ava Protocol's ecosystem involve risks specific to early-stage blockchain protocols, including smart contract risk, regulatory risk, and liquidity risk.





